Nouvelle Produits
-
Promo !

Tops, chemises | ONAC TOP Top en mesh imprimé Noir | Cop Copine Femme
€ 30.03€ 19.11 Choix des options -
Promo !

Robes | ADIUS ROBE Robe courte à volant Soleil | Cop Copine Femme
€ 129.68€ 67.34 Choix des options -
Promo !

Jupes, shorts | POUPA JUPE Jupe courte jaune soleil Soleil | Cop Copine Femme
€ 76.44€ 37.31 Choix des options -
Promo !

Accessoires, chaussures | SURA CABAS Cabas imprimé Imprime Blanc | Cop Copine Femme
€ 43.68€ 26.39 Ajouter au panier -
Promo !

Tops, chemises | ARLUX DEBARDEUR Débardeur bi-matière noir Noir | Cop Copine Femme
€ 122.30€ 57.33 Choix des options -
Promo !

Vestes, manteaux | BASO VESTE Veste asymétrique à carreaux Carreaux | Cop Copine Femme
€ 146.97€ 76.44 Ajouter au panier -
Promo !
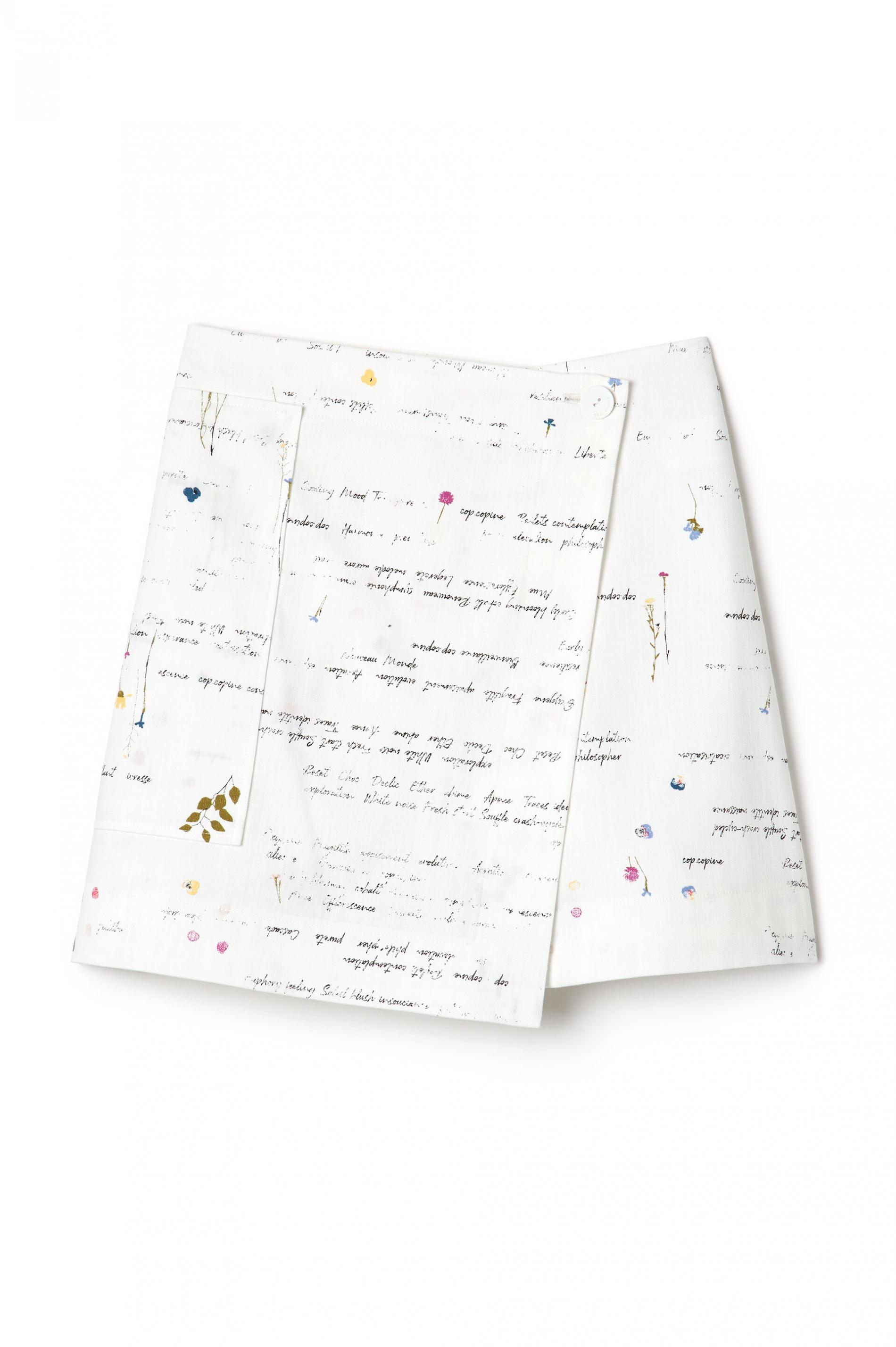
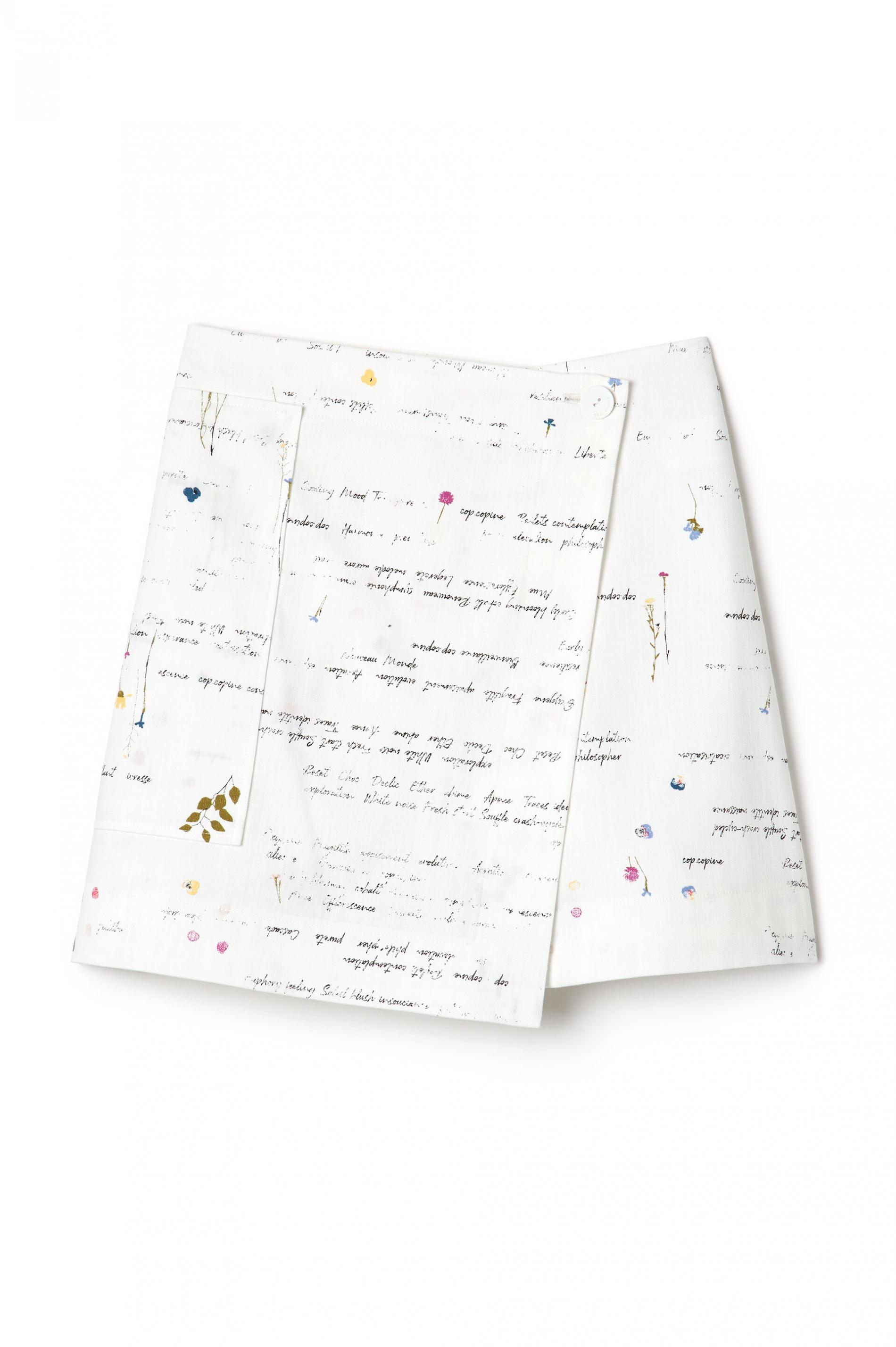
Jupes, shorts | TOMI JUPE SHORT Jupe-short imprimée Blanc | Cop Copine Femme
€ 81.90€ 53.69 Choix des options -
Promo !

Tops, chemises | ONAC TOP Top en mesh imprimé Sanguine | Cop Copine Femme
€ 32.03€ 19.11 Choix des options